Why small businesses need to be aware of the risk of ransomware
- Feb 16, 2023
- 4 min read
Many news stories about ransomware report about large-scale attacks on government departments or global companies such as Samsung and Microsoft, which may sound like it’s unlikely to happen to a small business in Bangor, Newport or Tenby. The reality is that it does happen here, and ransomware continues to threaten the businesses of Wales.
In 2022 alone, based on blockchain data, more than $457million was extorted by criminals through ransomware. The National Cyber Security Centre (NCSC) has also recently released a report stating that ransomware is one of the greatest threats to the charity sector, but it still poses a significant threat risk to ALL businesses in every sector.
The Cyber Resilience Centre for Wales (WCRC) invited board member Craig Gillespie, public sector operations specialist at Chainalysis to discuss the rise of ransomware, how attacks happen, things to be aware of and protecting your business.

What is ransomware?
Ransomware is a type of cyber-attack that focuses on gaining unauthorised access to an organisation with the ultimate aim to execute malicious software, also known as malware. The malicious software is used to encrypt data and prevent access to business-critical information, thus impacting the day-to-day operation of the business or organisation.
More recently there is a trend for criminals to also steal data in order to ‘double extort’ a victim by not only encrypting it, but threatening to release data if a ransom is not paid.
What is the cost of ransomware?
I work for Chainalysis, which specialises in blockchain data analysis, and our yearly findings have been released relating to the illicit cost of ransomware.

These findings represent the absolute minimum and note that true totals are likely to be much higher. This is because there are many cryptocurrency addresses controlled by ransomware attackers that are yet to be identified and incorporated into these figures.
Whilst the ransomware payments have reduced from $766million in 2021 to $456milion for 2022, this does not mean that attacks are down. We believe that much of the decline is simply due to victims’ organisations refusing to pay ransomware attacks and not because there are less victims.
So does this mean I should be less concerned about ransomware?
No, the threat of ransomware is just as serious as it has ever been. In fact there is no evidence that there is a decline in the number of attacks despite ransomware revenue falling.
What we are seeing is that ransomware attackers are now increasingly trying to obscure their efforts.

The average span of an individual type of ransomware, known as a ransomware strain, is now just 70 days long. Attackers are frequently changing the type of ransomware that they are using in efforts to both increase their chances of success, but also to frustrate attempts to trace those responsible.
Who is behind these ransomware attacks?
The constant turnover amongst top ransomware strains and appearance of new ones would suggest that the ransomware world is a crowded one, with criminal organisations competing against one another. However, this is not the complete picture. While many strains are active throughout the year, the actual number of individuals who make up the ransomware ecosystem is likely quite small.
One place Chainlaysis has seen this is in affiliate overlap. Most ransomware strains function on the ransomware-as-a-service (RaaS) model, in which the developers of a ransomware strain allow other cybercriminals, known as affiliates, to use the administrator’s malware to carry out attacks in exchange for a small, fixed cut of the proceeds.
Chainalysis has been able to use blockchain data to show that many affiliates carry out attacks for several different strains. So, while dozens of ransomware strains may technically have been active throughout 2022, many of the attacks attributed to those strains were likely carried out by the same affiliates. We can think of it in the same way that a rideshare driver may have their Uber, Lyft, and Oja apps open at once, creating the illusion of three separate drivers on the road — but in reality, it’s all the same car.

We also saw the recent example of the National Crime Agency and Office of Financial Sanctions and Implementation issuing sanctions against seven individuals who have been involved in the proliferation of ransomware.
These individuals were not high-level administrators – they’re the worker bees who do the development work. They’re more junior people who probably thought they would largely escape scrutiny because they don’t actually launch attacks themselves.
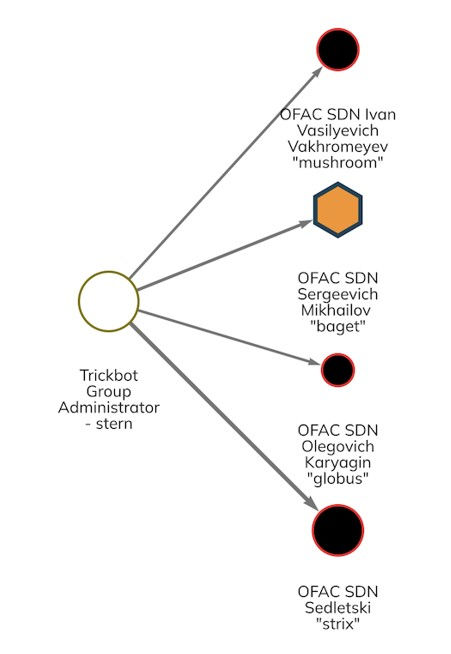
The message that is sent with these designations is that no one involved in the ransomware supply chain is safe. Whether you’re an administrator, a developer, an affiliate, a services provider, or an exchange laundering ransomware funds, the transactions are captured on the blockchain, and investigators can identify them. The key to disrupting ransomware is to disrupt this supply chain.
How to protect your business
The first critical step is placing cyber security on the agenda of your business. The WCRC focusses on breaking things down into steps and priorities to help people reduce threats through practical, comprehensible and simple actions. The WCRC is a police-led resource so anyone in contact with the centre is in a safe and friendly space to engage in conversation and debate.
As a member of the WCRC you’ll join a community of businesses all of which are supported by the centre’s excellent partnerships with local police forces, universities, advisory group, trusted partners and wider business network.
WCRC free membership benefits:
● National Cyber Security Centre (NCSC) guidance - how organisations can protect themselves in cyberspace, including the 10 steps to cyber security from the government NCSC division.
● NCSC’s Exercise in a Box – a tool to give your organisation a ‘dummy’ run of a cyberattack. Similar to testing your fire drill. Tailored for different sized organisations.
● NCSC board toolkit - resources designed to encourage essential cyber security discussions between the board and their technical experts.
● Regular newsletter updates – informing members on all the latest news and commentary on cyber risks and threats and how to stay resilient against them.
If free membership is of interest to you, it takes just a few moments to sign up, alternatively contact our team if you’d like to discuss your cyber challenges in more detail.
Where can I find out more about cryptocurrencies?
Chainalysis produces regular blogs on a variety of cryptocurrency related topics that can be accessed here. It also has an academy with a host of free content to help you learn more about cryptocurrencies, you can find out more here.
Chainalysis will soon release the 2023 version of the Crypto Crime Report which breaks down a variety of trends related crypto currency crime, you can reserve your free copy here.




Comments